First published 07 April, 2024
African nations’ data protection laws are, to some extent, weaker compared to Europe’s. This is because the European Union’s (EU’s) General Data Protection Regulation (GDPR) sets a high standard for digital data protection. We can think of the GDPR as a benchmark for strong data protection laws. Moreover, African countries have varying levels of success in putting their data protection policies into practice. Digital governance policies in Africa can shape the continent’s progress as digital advancements grow alongside economic development.
This is why current data governance across African states must be assessed, particularly paying attention to their trends and differences. While South Africa, Kenya, and Botswana have seen rapid growth in data protection policies, they still need to catch up to the GDPR standards of the EU.
But why is this important?
Between 2020 and 2023, over 30 African countries implemented data protection laws. As expected, each new regulation brings fresh compliance obligations and penalties for non-compliance.
Next Wave continues after this ad.
![The State of Tech in Africa]()
The first quarter of 2024 is just over and there was a lot of activity within Africa’s Tech Ecosystem in that period.
Due to varying reasons, some startups had to trim their workforce while there were others who even expanded into new territories. A couple of interesting M&A deals have also occurred.
Come and get an exclusive scoop into the details of these and more, like funding deals, at a specially curated edition of TechCabal Live on April 12 by 11am (WAT). You will also witness the State of Tech in Africa Q1 2024 report launching.
The report spotlights important trends in Q1 2024 while also delving deeper into the nitty gritty of various happenings in Africa’s Tech Space.
As a stakeholder in Africa’s Tech Ecosystem, these insights will help you position strategically and uniquely to harness the innovative progress within this sector. You don’t want to miss this.
Register here now to make sure!
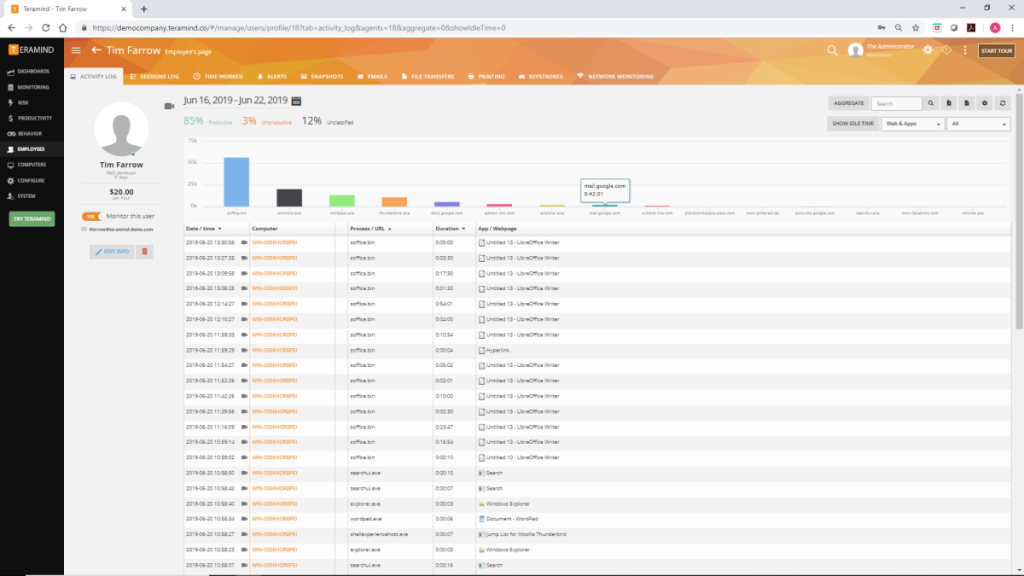
This, therefore, means that organisations with operations or customers in Africa must understand the applicable laws fully. Many internet-based businesses operate or use cloud services in multiple African nations; this sometimes calls for transferring personal data across borders. This movement often occurs between African countries and regions such as the EU, UK, US, and Australia, which can pose various data protection challenges.
Understanding the importance of data privacy rules in each African country, especially limitations on data transfer, cannot be stressed enough. Organisations must also check if local laws limit using service providers within African nations and their related requirements. A grasp of the legal framework for transferring personal data from African countries is essential for compliance.
Partner Content:
Read: How to solve the problem of financial inclusion in Nigeria
here.
Circling back to GDPR and the EU…
Considering Europe’s stringent directive that international players adhere to its data protection standards, we must ask whether European companies maintain the same standards when handling personal data from Africans as they do with Europeans.
Next Wave continues after this ad.
![DICE: The Tech Ecosystem Mixer]()
On April 26th, H.M Hannatu Musa Musawa, the Minister for Art, Culture & the Creative Economy, alongside distinguished experts, will speak at the DICE Ecosystem Mixer 2.0, with a focus on Africa’s creative economy.
Register here for a chance to attend.
This research revealed disparities in digital rights granted by subsidiaries of European telecom giants Orange and Vodafone in Senegal and Kenya compared to their European counterparts. The discrepancies included lack of transparency in publishing terms of use for prepaid services, minimal disclosure regarding data collection practices, third-party access, and security measures.
This highlights how, despite the principles underpinning the European data protection regime, companies may exploit regulatory gaps in countries to their advantage, compromising data privacy standards.
Many Western tech companies are notorious for disregarding user data privacy, offering convenience at the expense of the vast amounts of personal data they harvest. This trend is due to the absence of markets where individuals can understand the value of their data, leading them to exchange it for minimal gains. This issue is common in Africa and less so in Europe, where the GDPR exists.
Consider the case of Worldcoin, supported by OpenAI’s CEO, Sam Altman, which uses blockchain technology to store biometrically derived tokens. It retains personal data indefinitely without allowing users to delete their information.
When Worldcoin launched its services in Kenya, it incentivised people with around $50 to get them to scan their irises. Despite concerns about data protection, Kenya initially licensed Worldcoin’s operations. Before its suspension in August 2023, Worldcoin had become very popular, scanning the irises of up to 350,000 Kenyans, most attracted by the monetary incentive. While these funds may temporarily alleviate financial constraints for locals participating in the exercise, there is a compelling argument that Worldcoin’s model is exploitative.
The other day, Worldcoin was temporarily banned in Portugal, following similar restrictions in Spain, leaving Germany as its sole European market for biometric data collection. Portugal’s data protection office imposed the ban after complaints about scanning children’s irises.
This case underscores Europe’s stringent stance on digital data protection. EU data protection laws afford individuals rights over their data, including the ability to edit or delete it. This was an obvious legal conflict with Worldcoin’s approach, highlighting the split in digital privacy standards between Africa and Europe.
Partner Content:
Read: Huawei Cloud to empower 100 Nigerian startups to boost cloud market.
here.
Bottom line
African nations must tailor data protection laws to their needs and enforce them consistently.
While directly copying the GDPR may not work, Africa can learn from the EU’s approach to demand global compliance. Despite initial uncertainties, harsh fines on non-comp
!–Subtitle>